On March 25, 2026, the RBI's Department of Supervision issued Advisory No. 3/2026 on Best Practices Relating to Customer Data Protection ('Data Protection Advisory'). It has not been publicly released - but Consentin managed to obtain a copy.
It is easy to skim this as a standard RBI non-binding advisory. This is a mistake.
The Data Protection Advisory is the clearest signal RBI has given on what it expects an RE's data protection architecture to look like under DPDP. In the process, the RBI makes several concrete, ops-heavy demands of REs.
This piece pulls out the 8 things REs should take away from the RBI Customer Data Advisory.
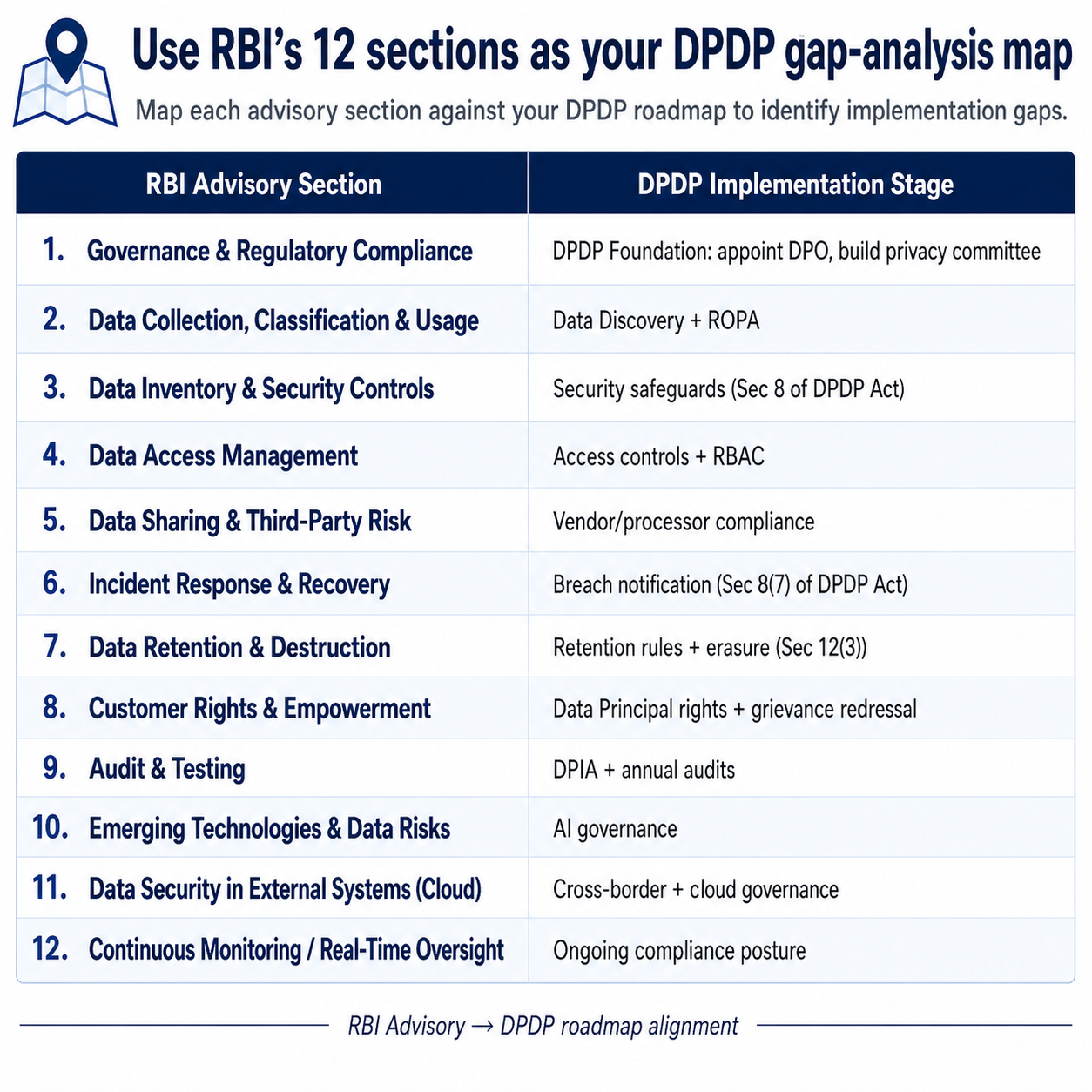
1. Validate your DPDP roadmap against the advisory's 12 sections
Many REs are waiting for a separate, RBI-specific DPDP rulebook before acting.
With this advisory, that wait is over.
The advisory is structured into 12 sections — that cleanly (and definitely not coincidentally) map onto the DPDP implementation roadmaps that REs are anyway implementing:
Governance → Data Collection & Classification → Data Inventory & Security → Access Management → Third-Party Risk → Incident Response → Retention & Destruction → Customer Rights → Audit & Testing → Emerging Tech → Cloud → Continuous Monitoring.
REs can now do a "gap analysis" of their DPDP roadmaps against this RBI customer advisory — and plug gaps.
What to do: Compare your DPDP roadmap with the advisory's 12 sections. Mark what's covered and where the gaps are.
2. Data Discovery + Data Mapping must now be fully automated
Industry conversations conducted by Consentin with DPOs and CISOs across BFSI consistently surface data inventories ranging from 700 to over 10,000 systems.
Many REs today run periodic data discovery scans across these systems and then plan to label/map them via separate largely manual processes.
The advisory explicitly rules this out.
Sec 2(a) of the Data Protection Advisory specifically asks REs to use automated tools for data tagging and classification across all RE systems.
This means automated data discovery AND automated data mapping — ideally all in one flow.
The RBI advisory is a blessing in disguise for teams in charge of this — as it gives them a clear justification to push for budgeting for fully automated data discovery + mapping tools.
What to do: Your legacy Data Discovery tools only do half the process automatically. Replace or upgrade them to ensure that they also perform automated data mapping. Allocate tooling budget if needed.
3. Centralise consent across all customer channels
Sec 2(b) asks for centralised mechanisms or platforms to capture, track, update, and manage customer consent in a consistent, auditable, and transparent manner across all relevant channels.
The key here is the word centralised.
Most REs run consent collection per channel today. One mechanism on the website, another in the app, another on agent devices, another at the branch. Each silo has its own audit logs — and they don't talk to each other.
The RBI Advisory wants to put an end to such per-channel silos.
Consent infrastructure has to be one inter-linked system across the organisation.
What to do: Audit every customer channel where consent is collected today. Consolidate onto a single consent management platform with a unified log, dashboard, and update mechanism.
4. Bring agent devices under MDM
Across recent industry sessions conducted by Consentin, BFSI CISOs identified that "agent devices" are the no. 1 data visibility gap.
Customers regularly share personal details, screenshots of KYC documents, photos and forms with agents on Whatsapp or SMS. Central teams have no way to track or control this.
Sec 4(b) of the RBI advisory specifically addresses this by asking for MDM solutions that enforce device encryption, secure data containers, remote wipe, and restrictions on copy-paste and screenshots — on every endpoint that handles customer data.
This includes agent devices. DSAs, business correspondents, field collection agents, and surveyors handle customer data on personal phones every day.
What to do: Roll out MDM across all endpoints that touch customer data, including third-party agent devices. Build the rollout into your vendor contracts and onboarding flows so new agents come under MDM by default. This will not be easy.
5. Build operational monitoring on top of vendor contracts
Vendor governance in most REs today is a contract + periodic audit function. The vendor signs the DPA and MSA and the RE does nominal audits annually. If something goes wrong, the indemnity clause covers financial damage.
The RBI advisory wants REs to stop relying solely on contracts and instead move towards a more "programmatic" system of enforcing vendor compliance.
Sec 5(e) asks for automated monitoring and alerts on third-party handling and modification of customer data.
Sec 5(f) asks for technical safeguards — not just contractual ones — to prevent third parties from storing sensitive customer data in plain text.
What to do: Add an operational monitoring layer to your vendor management. Specify automated alerts on data access, modification, and storage in vendor contracts. Build technical verification — not just self-attestation — into onboarding and renewal. This will not be easy.
6. Make data protection a Board-level, multi-department responsibility
Section 1 of the advisory makes three asks together:
- Sec 1(b): Customer data security and privacy as a standing Board-level agenda item, reviewed quarterly or semi-annually, with key incidents and remediation progress.
- Sec 1(d): A RACI matrix for customer data protection — Responsible, Accountable, Consulted, Informed — across all relevant functions.
- Sec 1(e): A cross-functional steering committee comprising business, technology, information security, legal, compliance, and other relevant functions to oversee customer data governance.
Read together, these asks mean that data protection stops being a compliance-and-CISO only function.
The RBI now wants business heads to be an active part of the DPDP/privacy compliance process — via a cross-functional steering committee that has board level backing.
For DPOs and CISOs who have spent the last two years trying to get business stakeholders to engage on privacy, RBI is now echoing your views.
What to do: Setup a central cross-functional DPDP/Data Protection Committee consisting of multi-department heads from various departments. Have this committee prepare an RACI matrix.
7. Redesign customer-facing breach response
Sec 6(c) asks REs to notify affected customers through SMS, email, app alerts, calls, and website updates — combined with active remediation guidance like password resets, credential blocking, and helpline support. These practices need to be integrated into the Cyber Crisis Management Plan.
Most CCMPs today handle regulatory notifications well — but typically via a single channel — like a generic SMS.
The RBI advisory wants multi-channel notifications for any data incidents or breaches. SMS, Email, Whatsapp, Calls. Basically try reaching the customer on all possible channels in case of any data incidents or breaches.
What to do: Audit your CCMP for the customer-facing leg. Build templates and workflows for SMS, email, app, calls, and website across breach scenarios. Pre-build the helpline scaling plan. Test it in your next cyber drill.
8. Build full audit trails for deletion and modification events
Sec 7(d) asks for robust audit trails for customer-data deletion and modification events — including approvals, user identity, timestamps, source/system details, and other relevant logs.
This is the heaviest operational leg of DPDP compliance — yet severely underbudgeted in most REs.
Personal data does not sit in one system. It sits in the LOS, the CRM, the data warehouse, vendor systems, agent devices, and unstructured locations like shared drives and email attachments.
When a customer comes to you and says "withdraw consent for use of email ID for marketing" — this request needs to be translated and communicated to all relevant systems:
- The email marketing system needs to be told to stop using the data
- The CRM needs to be told to stop syncing this into email lists
- Marketing teams must be told to delete this from spreadsheets
- But, the LMS and CBS must retain the email — as it may be needed for, say, account servicing or repayment communications
And each communication will need a clear audit trail + confirmation message.
Essentially, you need a system that can translate a customer data request into a detailed and accurate set of instructions that your downstream systems can action. This then needs to be recorded in a clear audit trail.
This needs to be reliably performed for each data request — across near infinite permutations and combinations.
What to do: You need to implement full-stack withdrawal and retention orchestration into your systems. Customer requests need to translate into action in downstream systems — with requisite audit trails generated.
Bonus Takeaway: RBI mentions AI — but that's about it.
It is 2026. An RBI advisory on customer data protection has to mention AI somewhere.
Sec 10(a) of the Data Protection Advisory asks REs to put "appropriate governance, monitoring, and risk mitigation mechanisms" on AI/ML use cases involving customer data — "commensurate with the use case and associated risks."
Across recent industry sessions conducted by Consentin with DPOs and CISOs, no participant has reported a mature, operational AI governance policy. Many said "we will wait for RBI guidance".
But RBI does not seem to be interested in giving detailed guidance yet and is instead nudging REs to formulate policies on their own.
What to do: Start actively formulating a detailed AI Governance Policy. Don't wait for RBI guidance.
TL;DR — your takeaway checklist
- Run a gap analysis: map the advisory's 12 sections against your DPDP roadmap. Plug the gaps.
- Replace or upgrade your data discovery tools to do automated labelling and mapping end-to-end. Allocate tooling budget.
- Consolidate consent collection across all channels onto one centralised platform.
- Roll out MDM across every endpoint that handles customer data — including third-party agent devices.
- Add automated monitoring and technical safeguards (not just contractual ones) to your vendor management.
- Set up a cross-functional Data Protection Committee with named members from business, tech, infosec, legal, and compliance. Build a RACI.
- Redesign your CCMP's customer-facing leg: SMS, email, app, calls, website. Pre-build templates and workflows.
- Build full-stack withdrawal and retention orchestration. Customer requests must translate into auditable actions across all downstream systems.
Bonus: Start drafting your AI governance policy now. RBI is not going to give you one.
This piece is informed by ongoing industry sessions conducted by Consentin with DPOs, CISOs, and compliance leads across BFSI. Discussions are anonymised. This piece is not legal advice; consult your counsel for final interpretation.
For more context:

.png)
.png)